Under the NIS2 Directive (Directive (EU) 2022/2555) and related EU cybersecurity legislation, compliance requirements emphasize ongoing risk management and supply chain oversight. Organizations subject to NIS2 must implement comprehensive cybersecurity measures and maintain robust incident reporting capabilities.
This article outlines the actual requirements from NIS2, distinguishing between explicit legal obligations and practical implementation approaches that may help organizations demonstrate compliance.
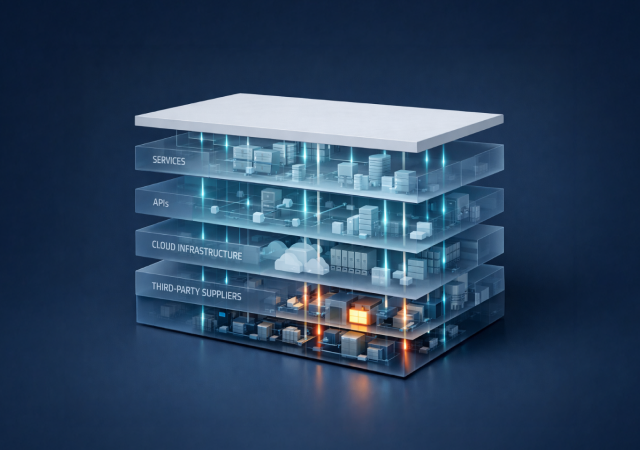
1. Supply Chain Security and Risk Assessment
NIS2 Requirements (Article 21)
Article 21(2)(d) of the NIS2 Directive explicitly requires entities to implement "supply chain security, including security-related aspects concerning the relationships between each entity and its direct suppliers or service providers."
Article 21(3) further specifies that entities must "take into account the vulnerabilities specific to each direct supplier and service provider and the overall quality of products and cybersecurity practices of their suppliers and service providers, including their secure development procedures."
This means organizations need to:
- Identify and document relationships with direct suppliers and service providers
- Assess vulnerabilities specific to each supplier
- Evaluate the overall quality of suppliers' cybersecurity practices
- Consider suppliers' secure development procedures
- Take into account coordinated security risk assessments of critical supply chains (Article 22(1))
Practical Implementation Approaches
While NIS2 doesn't prescribe specific methodologies, many organizations find it helpful to:
- Map digital connections and dependencies with suppliers (e.g., APIs, integrations, data flows)
- Prioritize supplier risks based on business criticality and exposure
- Maintain documentation showing how supplier assessments were conducted
- Track changes in supplier risk posture over time
While not mandated by the directive, "proximity-based" prioritization provides a technical pathway for organizations to fulfill NIS2 mandates for ongoing oversight and proof of dependency mapping. At ThingsRecon, we do this with our proprietary measure of Digital Proximity (Patent Pending), analyzing the degree to which a third-party is technically, operationally, and contextually integrated into an environment. This way, organizations can identify which connections touch their "crown jewels" and essential services, allowing security teams to move beyond generic industry scores and produce the defensible, risk-based assessments and targeted mitigation measures required by the EU package.
Ultimately, this approach ensures that a "medium" vulnerability on a deeply embedded supplier is correctly prioritized as critical, directly supporting the NIS2 goal of protecting the resilience of critical infrastructure.
2. Incident Reporting Obligations
NIS2 Requirements (Article 23)
Article 23 establishes clear incident reporting requirements with specific timelines:
What Must Be Reported (Article 23(3)):
Significant incidents that:
- Have caused or are capable of causing severe operational disruption or financial loss, or
- Have affected or could affect others by causing considerable material or non-material damage
Reporting Timeline (Article 23(4)):
What to Include in Reports (Article 23(4))
Early Warning must indicate:
- Whether the incident is suspected of being caused by unlawful or malicious acts
- Whether it could have a cross-border impact
Incident Notification must include:
- Initial assessment of the incident, including severity and impact
- Indicators of compromise, if available
- Any relevant information on cross-border impact
Final Report must provide:
- Detailed description of the incident and its severity/impact
- Type of threat or root cause that triggered the incident
- Applied and ongoing mitigation measures
3. Cybersecurity Risk-Management Measures
NIS2 Requirements (Article 21(2))
Article 21(2) requires entities to implement measures based on an "all-hazards approach," including at minimum:
- (a) Policies on risk analysis and information system security
- (b) Incident handling
- (c) Business continuity, backup management, disaster recovery, and crisis management
- (d) Supply chain security (as detailed above)
- (e) Security in network and information systems acquisition, development and maintenance, including vulnerability handling and disclosure
- (f) Policies and procedures to assess the effectiveness of cybersecurity risk-management measures
- (g) Basic cyber hygiene practices and cybersecurity training
- (h) Policies and procedures regarding the use of cryptography and, where appropriate, encryption
- (i) Human resources security, access control policies and asset management
- (j) The use of multi-factor authentication or continuous authentication solutions, secured voice, video and text communications and secured emergency communication systems within the entity, where appropriate
Monitoring and Oversight
Article 21(2)(f) requires organizations to establish "policies and procedures to assess the effectiveness of cybersecurity risk-management measures." While the directive doesn't mandate specific monitoring tools or real-time alerting systems, many organizations implement:
- Regular assessments of risk-management measure effectiveness
- Monitoring for significant changes in their risk environment
- Periodic reviews of supplier cybersecurity posture
- Documentation of assessment activities for regulatory oversight
4. Evidence and Documentation
Compliance Demonstration
While NIS2 doesn't explicitly use terms like "audit-ready evidence" or prescribe specific documentation formats, entities should be prepared to demonstrate compliance with the directive's requirements to competent authorities.
Practical considerations include:
- Maintaining records of risk assessments and management measures implemented
- Documenting supplier cybersecurity evaluations and the criteria used
- Keeping logs of incident detection, response, and reporting activities
- Retaining evidence of training programs and policy implementation
- Ensuring documentation can demonstrate the "appropriate and proportionate" nature of measures taken (Article 21(1))
Data Quality and Verification
NIS2 emphasizes that measures must be "appropriate and proportionate" and based on "the state-of-the-art" (Article 21(1)). Organizations should ensure that:
- Risk assessments are based on reliable, current information
- Supplier evaluations use verifiable data sources
- Incident reports contain accurate technical and impact information
- Documentation reflects actual implemented measures, not just policies
Specific methodologies like "confidence scores," "AI-driven verification," or proprietary data validation frameworks, while not required by NIS2, enhance the quality and reliability of compliance evidence.
For instance, ThingsRecon uses an agentic AI platform with multiple specialized agents to ensure that information—spanning 132 structured business intelligence fields—is cross-checked and validated against traceable source evidence to prevent hallucinations or guesswork.
This evidence-first model allows GRC teams to present trustworthy data with a high degree of confidence, directly fulfilling the NIS2 expectation for clear prioritization of suppliers that could impact critical services and providing the auditable proof of vendor oversight necessary for the Union's new cyber posture certifications.
5. Future Developments: EU Cybersecurity Certification
Proposed Cybersecurity Act 2 (CSA2)
On 20 January 2026, the European Commission proposed amendments to Regulation (EU) 2019/881 (the Cybersecurity Act), sometimes referred to as "Cybersecurity Act 2" (CSA2).
This proposal includes:
- Introduction of voluntary certification schemes for entities' "cyber posture"
- Potential to use such certificates as evidence of compliance with various EU cybersecurity requirements, including NIS2
- Harmonized approach to demonstrating cybersecurity maturity across the EU
Current Status:
- CSA2 is a legislative proposal subject to approval by the European Parliament and Council
- Expected adoption timeline: late 2026 or 2027
- Once adopted, implementation timelines will be specified in the final legislation
- This certification framework is NOT currently part of NIS2 and is NOT yet available
The road to NIS2 compliance
NIS2 establishes clear legal requirements for cybersecurity risk management, supply chain security, and incident reporting. While the directive provides flexibility in how organizations meet these requirements, it is specific about what must be achieved.
Therefore, security teams should focus on:
- Implementing the specific measures outlined in Article 21
- Establishing robust incident reporting processes per Article 23
- Documenting compliance efforts for regulatory oversight
- Staying informed about future developments in EU cybersecurity legislation
Legal References
Primary Legislation:
Directive (EU) 2022/2555 of the European Parliament and of the Council of 14 December 2022 on measures for a high common level of cybersecurity across the Union (NIS2 Directive)
Official Journal L 333, 27.12.2022, pp. 80-152
EUR-Lex: https://eur-lex.europa.eu/eli/dir/2022/2555/oj
Key Articles Referenced:
- Article 21 - Cybersecurity risk-management measures
- Article 22 - Coordinated security risk assessments of critical supply chains
- Article 23 - Reporting obligations
- Article 21(1) - General obligations for appropriate and proportionate measures
- Article 21(2) - Specific minimum measures required
- Article 21(3) - Supply chain security specifics
- Article 23(3) - Definition of significant incidents
- Article 23(4) - Reporting timeline and content requirements