Digital Proximity maps directly to the NIS2 Directive's requirement for identifying and securing key assets within the ICT supply chain. While NIS2 mandates that essential and important entities maintain high, shared cybersecurity standards to protect their services, Digital Proximity provides the technical mechanism to determine which specific supplier connections represent the highest risk to those services.
What is Digital Proximity?
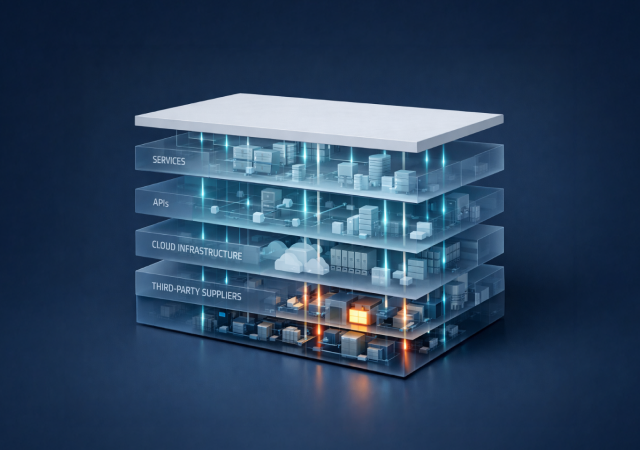
Digital Proximity is a patent-pending, proprietary measure developed by ThingsRecon that maps the real digital connections between an organization and its suppliers. Instead of assigning a generic security score to a vendor as an isolated entity, it measures how closely that vendor’s systems touch your production environments, identity layer, data flows, and operational core.
This is what makes it fundamentally different from traditional ratings.
How Can Organizations Use Digital Proximity to Meet NIS2 Asset Identification Requirements?
This key measure maps to NIS2 requirements across several critical areas:
1. Identification of Key Assets and "Crown Jewels"
The revised Cybersecurity Act and NIS2 emphasize the identification of key assets in the ICT supply chain to better understand vulnerabilities.
Correlation: Digital Proximity measures how directly a supplier’s systems touch an organization's most critical systems or "crown jewels". Instead of treating every supplier as a generic entry in a database, it identifies those that are deeply integrated into your operations, directly fulfilling the NIS2 mandate to identify "key" assets.
2. Evidence-Based Dependency Mapping
NIS2 and DORA require proof of dependency mapping and continuous oversight of supply chain risk.
Correlation: Most traditional tools provide generic vendor scores that do not reflect the actual digital relationship. Digital Proximity replaces these assumptions with actual digital links, surfacing hidden APIs, scripts, and certificates that touch production environments; thereby providing the "audit-ready evidence" and "dependency mapping" that regulators now expect.
3. Risk Prioritization for Essential Services
A core goal of the New Cybersecurity Package is to provide targeted mitigation measures based on thorough impact assessments.
Correlation: A high-severity vulnerability is often meaningless without the context of where it sits. Digital Proximity allows security teams to prioritize their top 100+ suppliers based on business impact. For example, a "medium" flaw on a payments provider touching production is categorized as more critical than a "critical" vulnerability in a forgotten test environment, allowing for the targeted mitigation required by EU rules.
4. Continuous Monitoring and Compliance
The NIS2 framework demands ongoing oversight rather than static, point-in-time assessments.
Correlation: Because your digital surface and your vendors' surfaces change constantly, Digital Proximity is integrated into a living map of risk. This allows GRC teams to demonstrate continuous, auditable proof of vendor oversight as the ecosystem evolves, ensuring they meet the legal obligations of the NIS2 and DORA frameworks.
5. Blast Radius and Concentration Risk
The EU factsheet highlights the need for Union-level coordinated risk assessments to identify vulnerabilities in specific ICT supply chains.
Correlation: Digital Proximity helps organizations understand the "blast radius" of a supplier event. By mapping how integrated a supplier is, organizations can assess the impact of third- and fourth-party connections, helping to identify concentration risks where multiple services rely on the same high-proximity provider.
NIS2 does not ask organizations to collect more questionnaires. It asks them to understand their dependencies and prove they are managing them.
By developing the Digital Proximity (Patent Pending) measurement, we translate that expectation into a technical model that maps real connections, prioritizes what truly matters, and turns compliance from a reporting exercise into an operational capability.
If you want to see how your supplier ecosystem actually connects to your critical systems, start with evidence, not assumptions. Request a demo of ThingsRecon to see it in practice.