The EU Cybersecurity Package introduced in 2026 strengthens how organizations identify, monitor, and manage ICT supply chain risk under frameworks like NIS2 and DORA. This article explains the package’s key pillars and how modern discovery and supply chain intelligence capabilities help organizations move from static compliance to continuous risk management.
The New Cybersecurity Package, introduced by the European Commission in January 2026, represents a significant legislative shift toward securing the Union's critical infrastructure and digital economy. With global cybercrime costs exceeding €9 trillion in 2025 and ransomware identified as the most impactful threat, the package provides a horizontal framework specifically designed to address security risks within the ICT supply chain.
Mapping the EU Cybersecurity Package to Technical Capabilities
By examining the core requirements of the EU package, we can map them to technical capabilities, specifically those utilized in Supply Chain Intelligence, to demonstrate how organizations can move from static compliance to evidence-based risk management.
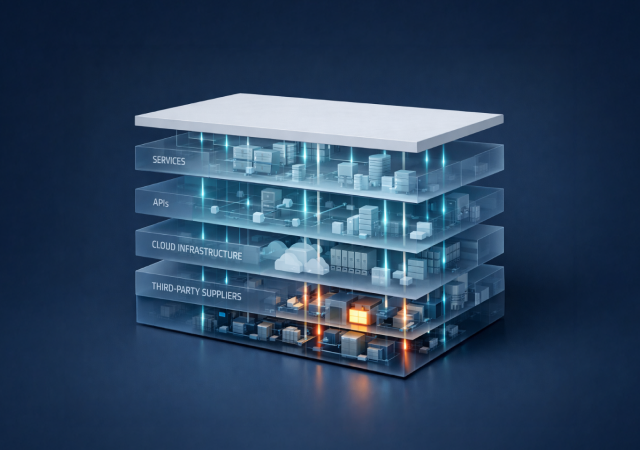
Pillar 1: Identification of Key Assets and Dependency Mapping
A central component of the Cybersecurity Act is the identification of key assets within ICT supply chains to better understand vulnerabilities. Traditional methods often fail here because they rely on documented inventories that frequently miss "shadow" connections.
• Mapping to Discovery Capabilities: The framework requires an exhaustive view of the digital surface. Deep, agentless discovery addresses this by pivoting from a single domain to map all connected assets, including subdomains, APIs, and scripts. Based on demos and customer results, this approach can uncover up to 50% more findings than standard scans, revealing the "invisible" links that attackers prioritize, like shadow AI tools or forgotten cloud buckets.
• Digital Proximity (Patent Pending): The EU package emphasizes the need to understand which components are critical. Using a proximity-based scoring model allows organizations to rank suppliers by how directly their systems touch "crown jewels". This provides the technical context required to determine if a vulnerability on a payment provider is a catastrophic risk or a minor hygiene issue.
Pillar 2: Coordinated Security Risk Assessments
The European Commission proposes Union-level coordinated security risk assessments to identify risks from third countries or high-risk suppliers. Useful capabilities to do so:
• Enrichment via Agentic BI: To meet these requirements, organizations must look beyond technical CVEs. By utilizing an army of over 200 AI agents, technical signals can be enriched with financial, geopolitical, threat intelligence, and compliance data. For instance, monitoring for a 30% drop in a supplier's headcount or changes in geopolitical standing provides the "narrative" necessary for board-level risk discussions mandated by the new package.
• Persona-Based SWOT Analysis: The EU package aims to simplify compliance for various stakeholders. A technical SWOT (Strengths, Weaknesses, Opportunities, Threats) analysis tailored to specific personas (such as the CISO, Procurement, or Legal) ensures that risk assessments are actionable for the specific department responsible for mitigation.
Pillar 3: Continuous Monitoring and "Blast Radius" Management
Under the NIS2 Directive and the revised Cybersecurity Act, there is an increased focus on continuous oversight and the ability to respond to incidents through CSIRTs (Computer Security Incident Response Teams).
• Living Maps vs. Static Lists: Compliance now demands more than annual snapshots. A living map of risk that refreshes signals (such as outages or data breaches) on a continuous basis allows organizations to maintain a "360-view" of their ecosystem.
• Blast Radius Analysis: During a major supplier event, such as a cloud provider outage, the EU package expects entities to understand their dependencies. Mapping the "blast radius" enables teams to identify not just direct third-party impacts, but also fourth- and fifth-party connections where a single point of failure could disrupt the entire chain.
Pillar 4: Certification and Evidence-Based Reporting
A major innovation in the 2026 package is the certification of an entity’s cyber posture to meet market needs and legal obligations.
• Audit-Ready Evidence: To achieve certification, organizations must move away from "guesswork" and toward evidence-backed reporting. Technical platforms can support this by providing timestamped evidence of SSL configurations, API security, and GRC signals, creating an auditable trail for regulators.
From Compliance to Resilience
The European Commission's New Cybersecurity Package signals the end of the "spreadsheet era" for third-party risk management. Compliance is no longer about maintaining documentation, but about demonstrating continuous understanding of your digital dependencies and the risks they introduce.
By aligning with a discovery-first model, enterprises can meet the rigorous demands of NIS2 and DORA, transforming compliance from a checklist into a strategic advantage that provides certainty.
Request a free Digital Proximity scan to discover hidden supplier connections in your environment.