The NIS2 deadline passed on 18 October 2024, enforcement is live and penalties are real. And yet, when we talk to CISOs, risk leaders, and security teams in training and advisory sessions, we hear that most organizations are still flying blind on their supply chain.
So what's happening between organizations that are trying to comply, and the suppliers they depend on?
The part most organizations are getting wrong: Supply chain security (and visibility)
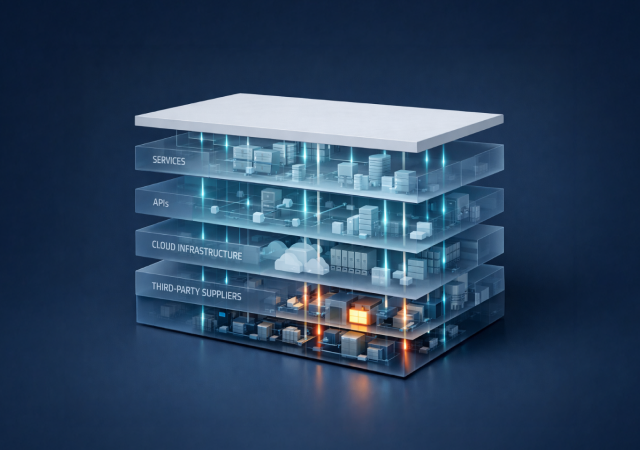
NIS2 has ten core cybersecurity risk management requirements under Article 21. One of them is supply chain security, explicitly named as a key obligation. This means companies must assess, monitor, and manage cyber risks across their entire value chain.
These requirements do not stop at your perimeter. They follow through your digital supply chain and create the need to understand and manage fourth-party risk: the vendors of your vendors.
That’s one obligation that most organizations are not close to meeting, not because they are negligent, but because they genuinely do not have the visibility to do so.
The average enterprise operates with 975 unknown cloud services, with only 108 known services being tracked by IT.
In practice, when we scan an organization's external digital footprint for the first time, the results consistently surprise the client. In a recent assessment for a major infrastructure organization in the transport sector, our initial scan surfaced 351 applications and 347 domains; they only knew about 50.
What we typically find that IT and security teams are unaware of:
- Shadow IT
- Forgotten sub-domains
- Third-party scripts still running on production systems
- Connected suppliers nobody had formally assessed.
The core problem for NIS2 compliance is that it requires organizations to take into account the vulnerabilities specific to each direct supplier and service provider, and the overall quality of their suppliers' and service providers' cybersecurity products and practices. An entity that does not take into account the results of coordinated risk assessments may be considered non-compliant even if it has fulfilled all other Article 21 requirements, and may face financial penalties as a result.
You cannot assess a supplier's vulnerabilities if you do not know that supplier is connected to you. And right now, most organizations do not know.
Why existing TPRM tools do not close this gap
Many organizations believe they are addressing their NIS2 supply chain obligations because they have a Vendor Risk Management (VRM) or Third-Party Risk Management (TPRM) program. Often, that program is built on questionnaires, self-reported assessments, and point-in-time security ratings from platforms that rate suppliers using a letter grade or numerical score.
NIS2 does not ask for a score. It asks for continuous, evidence-based visibility into supplier risk.
A vendor risk score tells you that a supplier rated "C" this quarter. It does not tell you that this supplier has a live JavaScript tag running inside your customer portal, with write access to session data. It does not tell you that a subsidiary of that supplier (one you have never heard of) is sharing infrastructure with a company subject to sanctions. It does not tell you that the supplier's subdomain that points to your API is running an end-of-life TLS configuration.
Those are the things that matter for NIS2 compliance. And they require active discovery, not passive scoring. Simply having an ISO 27001 certificate from your vendor does not fulfil regulatory requirements.
Here’s a practical approach to achieve that “living map” view of supplier risk:
What actual compliance looks like
Based on what we are seeing, organizations that are making genuine progress on NIS2 supply chain compliance are doing a few things that others are not.
1. They start with discovery, not documentation
Before you can assess supplier risk, you need to know who your suppliers actually are, including the ones you have not formally onboarded. That means mapping what is connected to your environment from the outside in, the way an attacker would see it, as opposed to relying on a contract database or a self-reported vendor list.
2. They prioritize by Digital Proximity, not generic scores
Not all suppliers carry the same risk. A supplier with a live script running in your customer-facing application is categorically different from one that mails you paper invoices. Scoring and prioritizing by actual digital connection (proximity and access) is what allows you to allocate limited resources where they matter.
3. They move from point-in-time to continuous
NIS2 does not ask for an annual questionnaire. It asks for ongoing risk management. ENISA's Technical Implementation Guidance, published in June 2025, requires organizations to maintain a register of in-scope suppliers updated with regular risk management activity, including unscheduled reviews. This points to continuous monitoring of external supplier posture.
4. They map findings to the regulatory frameworks explicitly
When a finding lands in your SIEM or GRC platform, it should be mapped to NIS2 obligations (and DORA obligations for financial services entities). That mapping is what makes the compliance narrative coherent when regulators ask for evidence, and here’s how to achieve it.
5. They involve management
NIS2 places accountability at the executive level, so conversations about supply chain risk need to happen in the boardroom, not just the SOC. This is not something that can be delegated entirely to a security operations team.
So, what’s the best NIS2 compliance tool?
No tool makes an organization NIS2 compliant, because compliance is a governance and operational outcome, not a software product. What tools can do is give you the visibility you need to know what you are protecting, help you prioritize where to focus, and provide the evidence trail that regulators will want to see.
The hardest part of NIS2 supply chain compliance is not technical, it’s organizational. Getting procurement, legal, security, and executive leadership aligned around a new set of obligations is slow, political, and expensive. The technical part (finding out what’s in your digital ecosystem) is actually not that hard if you use the right approach.
In short: start with the outside view. Before you redesign your TPRM program, before you renegotiate supplier contracts or build the compliance documentation, find out what your external digital footprint actually looks like. Run a free scan with ThingsRecon and you will almost certainly find things you did not know were there. Those findings will be both your highest risk and your strongest argument for why this needs to happen now.